A kernel vulnerability that scales across Linux distributions
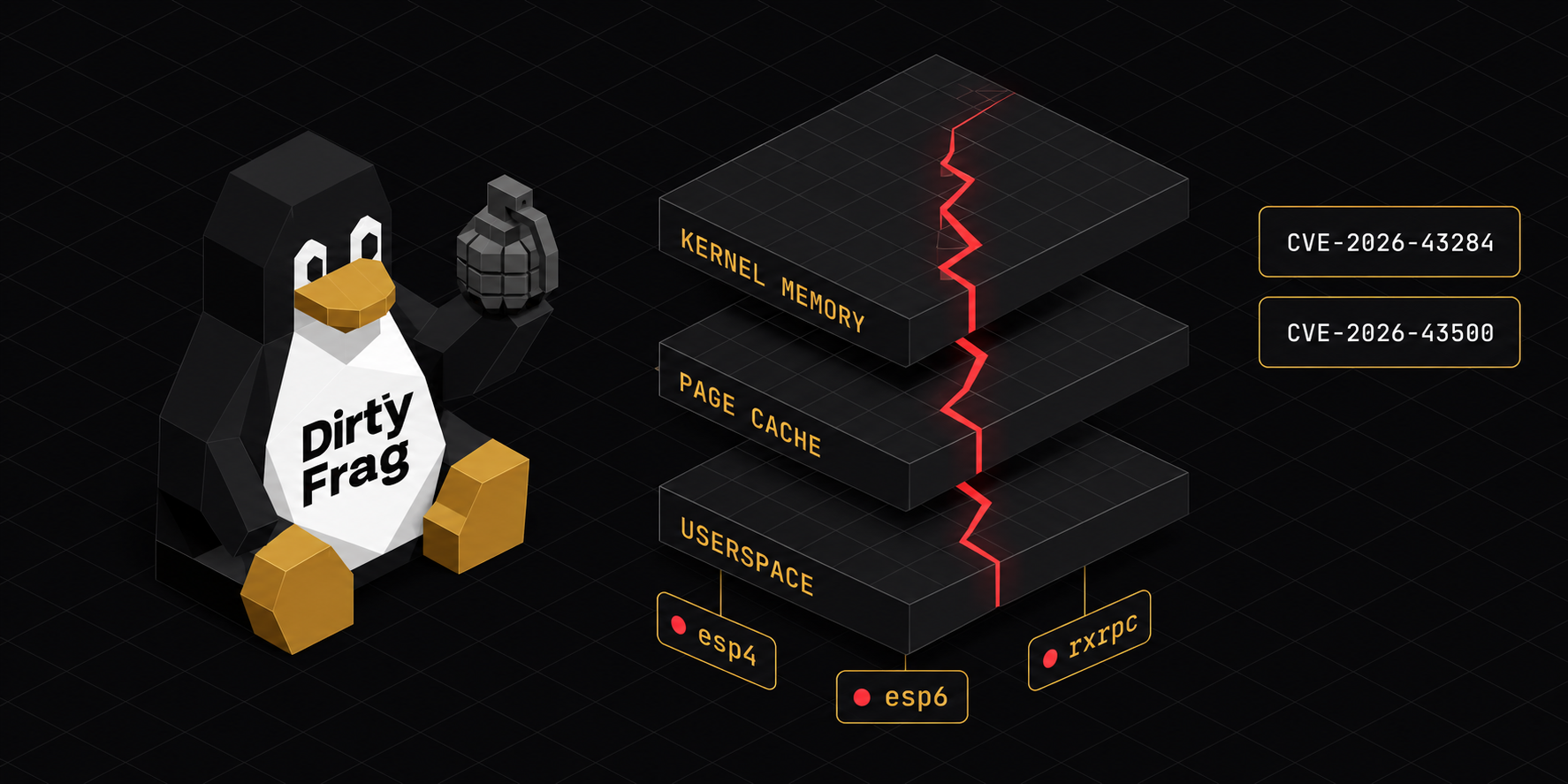
In early May 2026, a critical Linux kernel vulnerability was disclosed that allows unprivileged users to escalate privileges and gain root access on nearly every major Linux distribution. The vulnerability, called Dirty Frag, chains two page-cache write bugs to bypass kernel protections.
Unlike previous vulnerabilities of this class (Dirty Pipe and Copy Fail), Dirty Frag requires no race conditions, no timing windows, and no kernel panic fallback. The exploit has a very high success rate.
We've completed a full audit of our infrastructure, patched what we can, and implemented additional hardening to reduce attack surface. This post covers what Dirty Frag actually is, why it matters, and the concrete steps we and other teams should take right now.
What Dirty Frag does
The vulnerability chains two separate kernel bugs:
- xfrm-ESP Page-Cache Write vulnerability (CVE-2026-43284). Allows arbitrary 4-byte writes to kernel memory via IPsec operations. It requires the ability to create network namespaces, which is unprivileged on most systems but restricted via AppArmor on Ubuntu.
- RxRPC Page-Cache Write vulnerability (CVE-2026-43500). A similar page-cache write primitive via RxRPC kernel module operations. This one requires no namespace privileges and runs on systems where the first vector is blocked.
By chaining them, an attacker can target root on any major distribution: if they can't use one vector, they use the other.
"The effective lifetime of these vulnerabilities is about 9 years. Every system running an unpatched kernel from roughly 2017 onwards is at risk."
Which systems are vulnerable
If you're running any of these, you need to act now:
- Ubuntu 20.04, 22.04, 24.04 (all current and recent releases)
- RHEL 8, 9, 10 and derivatives (CentOS, AlmaLinux, Rocky)
- Fedora (current and recent versions)
- Debian and derivatives
- openSUSE Tumbleweed and Leap
The only systems fully protected right now are those running kernels with the patches already applied (mainline Linux as of May 5, 2026 includes a patch for CVE-2026-43284). But most distributions haven't backported fixes to stable branches yet, meaning most production systems are still exposed.
What we did to protect our infrastructure
Since no vendor patches exist yet for most distributions, we implemented defense-in-depth:
For our clients, this means:
- Unprivileged users cannot load the vulnerable kernel modules
- The attack vectors are eliminated even if a user finds a way around module loading
- We're monitoring upstream for vendor patches and will apply them as soon as they're available
What production teams should do today
You don't need to wait for vendor patches. Follow these steps to disable the vulnerable modules and eliminate risk:
- Create the modprobe configuration. This tells the kernel not to load the vulnerable modules even if something requests them. Use this command:
sudo tee /etc/modprobe.d/dirtyfrag.conf > /dev/null <<'EOF' install esp4 /bin/false install esp6 /bin/false install rxrpc /bin/false EOF - Unload the modules from the running kernel. If they're already loaded, remove them:
The second command clears the page cache. Both changes persist across reboots.sudo rmmod esp4 esp6 rxrpc 2>/dev/null sudo bash -c 'echo 3 > /proc/sys/vm/drop_caches' - Verify the modules are blocked. Check with:
You should see three lines, one for each module.cat /etc/modprobe.d/dirtyfrag.conf - Consider your use case. If your application uses IPsec (xfrm) or RxRPC, which is rare in most web servers, you have two options: either disable the modules and find an alternative networking approach, or restrict unprivileged namespace creation via AppArmor, SELinux, or sysctl. For most teams, disabling these modules is the cleaner solution.
- Watch for vendor patches. Linux distributions are backporting fixes now. Once a patch lands for your OS, test it in staging, then deploy to production through your normal update process. Mainline Linux already has patches available, so distribution kernels will follow soon.
For development and staging environments
The same mitigation applies, but you may want to test without disabling the modules to understand the impact if your code relies on IPsec or RxRPC.
Keep your testing environments patched just as soon as vendor patches are available. These are the places where your team can verify mitigation before deploying to production.
What this means for the broader ecosystem
Dirty Frag is severe, but it's also solvable without waiting for kernel patches. Unlike some vulnerability classes that require coordinated patching across the entire ecosystem, this one can be mitigated at the system level with a simple configuration change.
The key lesson: your security posture shouldn't depend entirely on the upstream vendor. Understand your infrastructure deeply enough to implement defense-in-depth on your own timeline.
"The teams that protected themselves weren't the ones waiting for patches. They were the ones who understood what modules they actually needed, disabled what they didn't, and moved on."
Moving forward
As patches become available from major distributions, we'll apply them in this order:
- Security-critical systems and production environments
- Development and staging servers
- All supporting infrastructure
We'll monitor the kernel mailing list and vendor security bulletins. Once vendor patches land, we'll verify they don't introduce regressions, then deploy them across our infrastructure.
If you're unsure whether your systems are affected, start with a simple check: log in and run the mitigation command. It takes seconds. It removes the risk entirely. That's a good trade.